Software Composition Analysis (SCA)
Source Repositories in Bytesafe retired
Bytesafe’s legacy Source Repository scanner reached end of life on July 31, 2024. SBOM management, analysis, and policy enforcement are now handled by SBOM Observer. This guide explains how Observer replaces the previous workflow.SBOM Observer makes SBOMs living assets - continuously enriched with context, validated against policy before delivery, and packaged with the evidence teams need to demonstrate compliance.
SBOM Management at Scale with Enterprise-Grade Assurance
SBOM Observer goes beyond traditional “generate and forget” SCA tools. It continuously analyzes SBOMs, enforces policies before code ships, and helps companies fulfill requirements from audits, regulators, and customers.
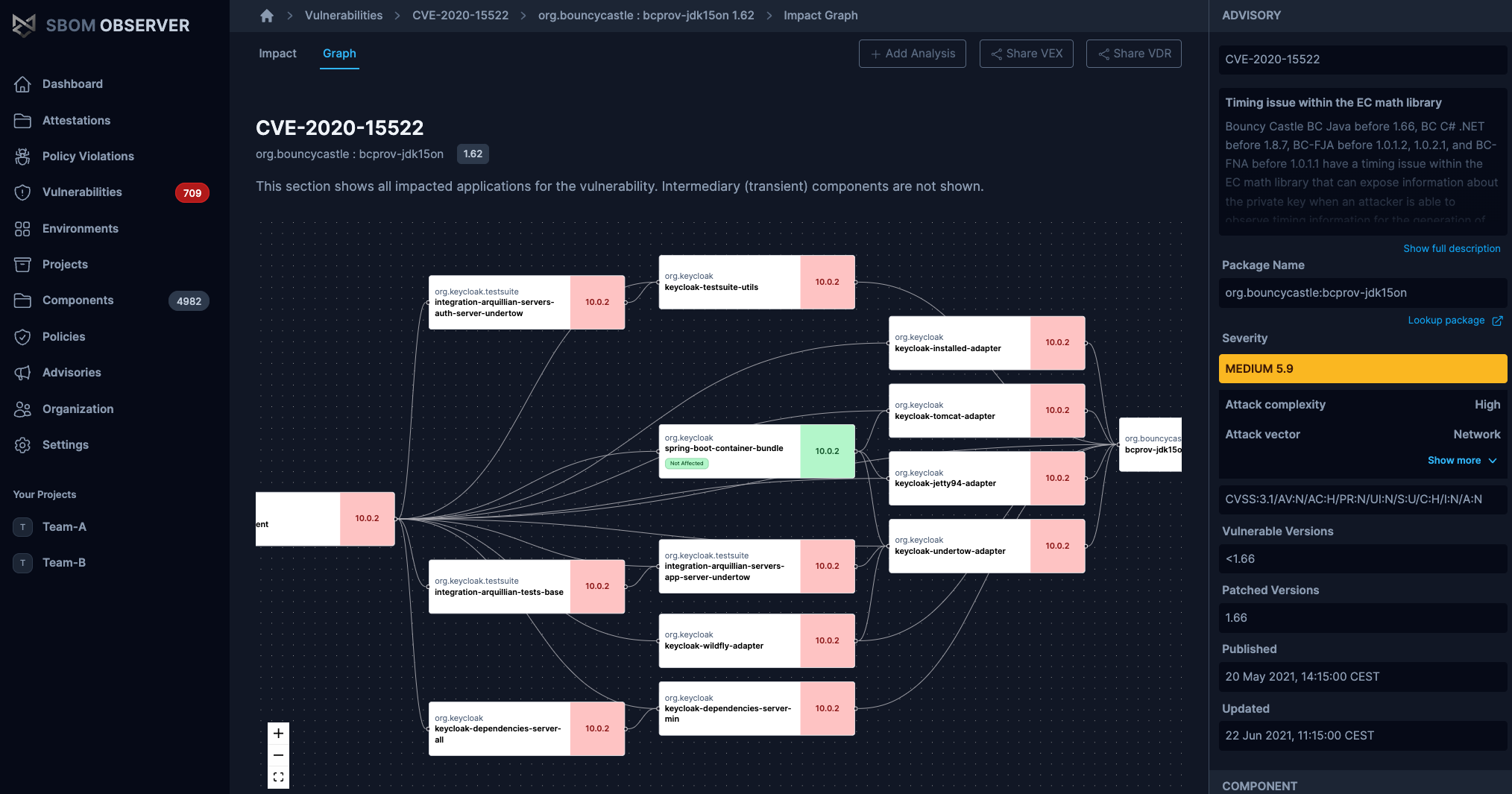
Continuous analysis & impact intelligence
Observer enriches SBOMs with live vulnerability data and dependency graphs so teams immediately see which services and releases are at risk. Everything is tracked across versions, while dashboards highlight what matters most. The result: faster triage and fewer false positives.
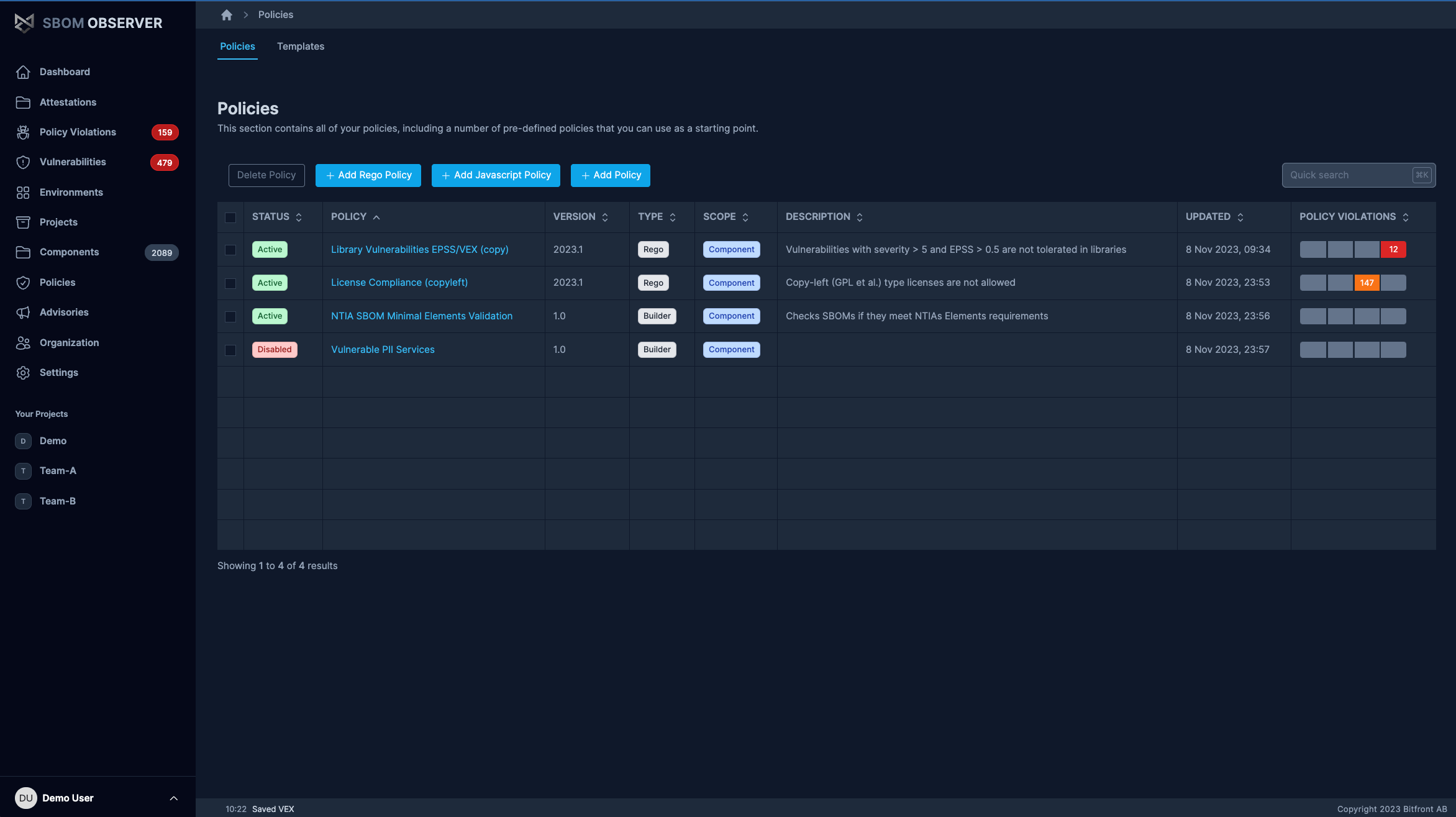
Reliable policy enforcement
Model frameworks such as DORA, CRA, NIS2, or your own customer controls, directly in the Observer policy engine. The Observer CLI validates every pipeline run, and keeps evidence tied to each release.
Evidence when auditors call
Observer collects VEX, VDR, SLSA provenance, and OpenSSF Scorecard data alongside each SBOM. Observer maintains a complete record of controls, artifacts, and risks, making it straightforward to prove compliance or share data with customers and regulators.
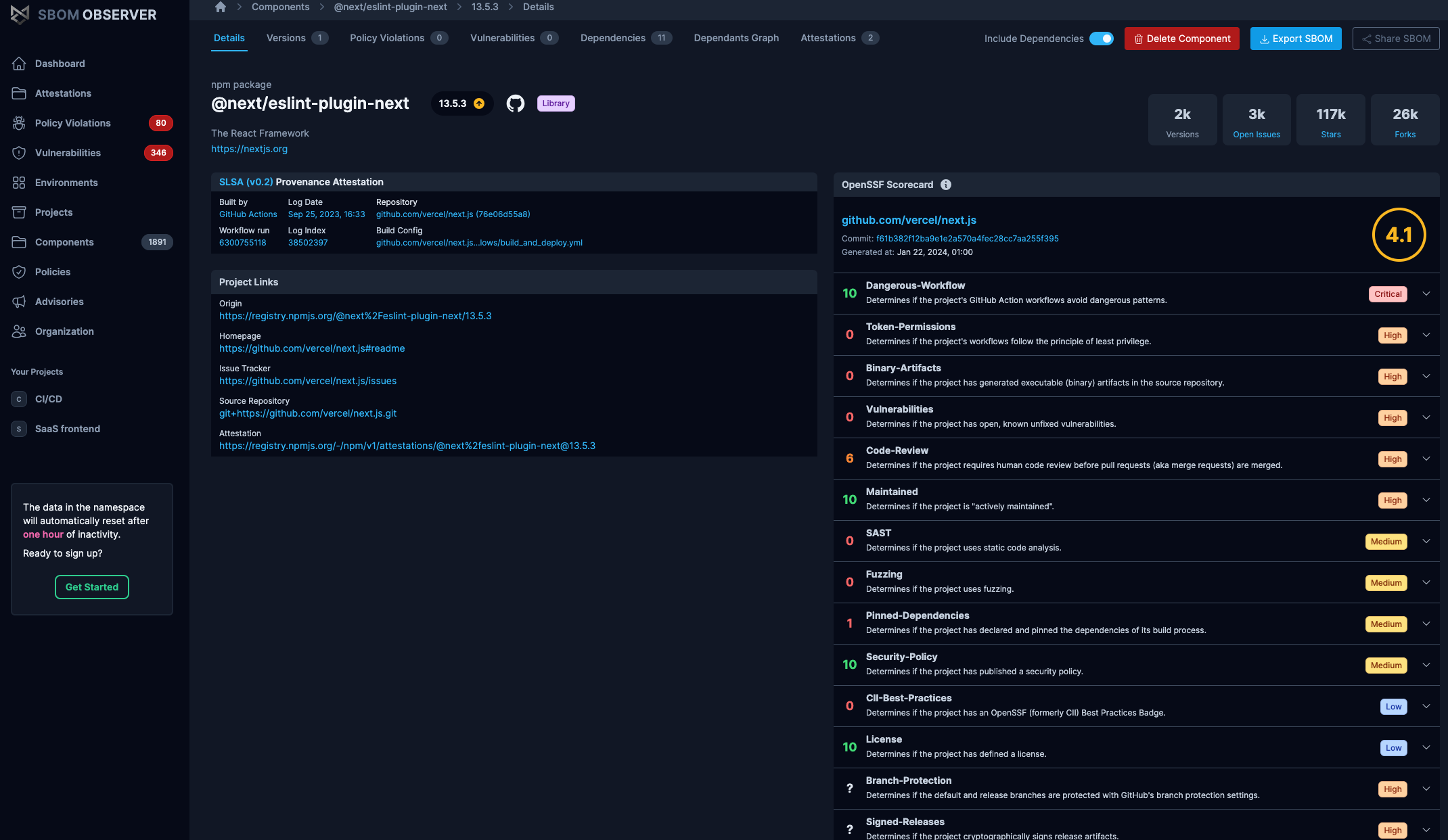
Designed for DevSecOps automation
Observer integrates directly into CI/CD through the open-source Observer CLI. Use it in GitHub Actions, GitLab, Azure DevOps, or Jenkins to generate and enrich SBOMs, enforce policy, trigger workflows when new risk is detected, and provide status codes to break builds on policy violations.
Get started with SBOM Observer
- Explore the platform: sbom.observer
- Automate workflows: Add the Observer CLI to CI/CD for enrichment and policy enforcement
- Request an introduction: Book a time via our Calendar